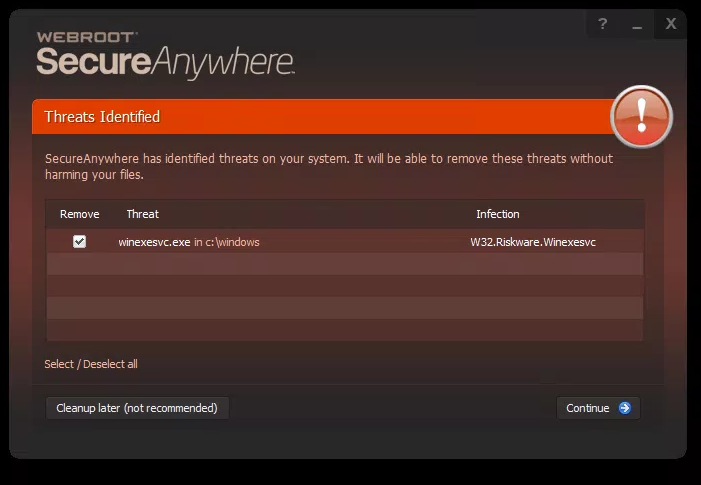
I'm seeing quite a few alerts detecting winexesvc.exe as w32.hack.tool.winexe this morning.
Is this a false positive - popped up on an otherwise not active PC after overnight's Windows updates?
Anyone else seeing this?
Edwin
Best answer by JesseBropez
View original