August 14th, 2014, 17:22 GMT · By Ionut Ilascu
Security researchers found evidence that the cybercriminal rings operating Boleto malware families adopted techniques used in Zeus Trojan for bypassing security solutions such as firewalls and web-filters.
It appears that these crooks cooperate on underground forums with their counterparts in Europe, those involved with Zeus Trojan in particular.
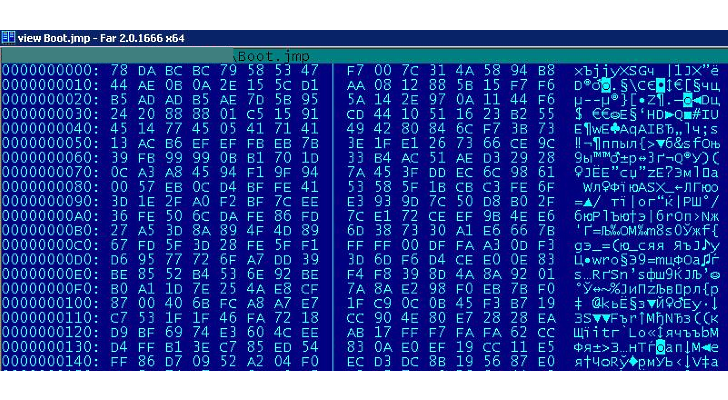
According to security experts from Kaspersky Lab, one of the newest tricks integrated by Boleto malware for increasing the rate of infections is to rely on non-executable payloads, which are actually portable executable (PE) files encrypted (XORed with a 32-bit key) and compressed using the ZLIB library.
Full Article
Login to the community
No account yet? Create an account
Enter your username or e-mail address. We'll send you an e-mail with instructions to reset your password.