********************************************************************
Microsoft Security Bulletin Advance Notification for August 2014
Issued: August 7, 2014
********************************************************************
This is an advance notification of security bulletins that Microsoft is intending to release on August 12, 2014.
The full version of the Microsoft Security Bulletin Advance Notification for August 2014 can be found at <https://technet.microsoft.com/library/security/ms14-aug>.
This bulletin advance notification will be replaced with the August bulletin summary on August 12, 2014. For more information about the bulletin advance notification service, see <http://technet.microsoft.com/security/gg309152>.
Microsoft will host a webcast to address customer questions on these bulletins on August 13, 2014 at 11:00 AM Pacific Time (US & Canada). Register for the Security Bulletin Webcast at <http://technet.microsoft.com/security/dn756352>.
This advance notification provides a number as the bulletin identifier, because the official Microsoft Security Bulletin numbers are not issued until release. The bulletin summary that replaces this advance notification will have the proper Microsoft Security Bulletin numbers (in the MSyy-xxx format) as the bulletin identifier.
https://technet.microsoft.com/library/security/ms14-aug
Daniel ;)
Microsoft Security Bulletin Advance Notification for August 2014 Issued: August 7, 2014
Userlevel 7
The following article is a update on Tuesday patches for IE and adobe.
(Microsoft Fixes Critical Vulnerabilities in Internet Explorer, Windows )
By Brian Prince on August 12, 2014 Microsoft and Adobe released a set of patches today to fix critical vulnerabilities in their products.
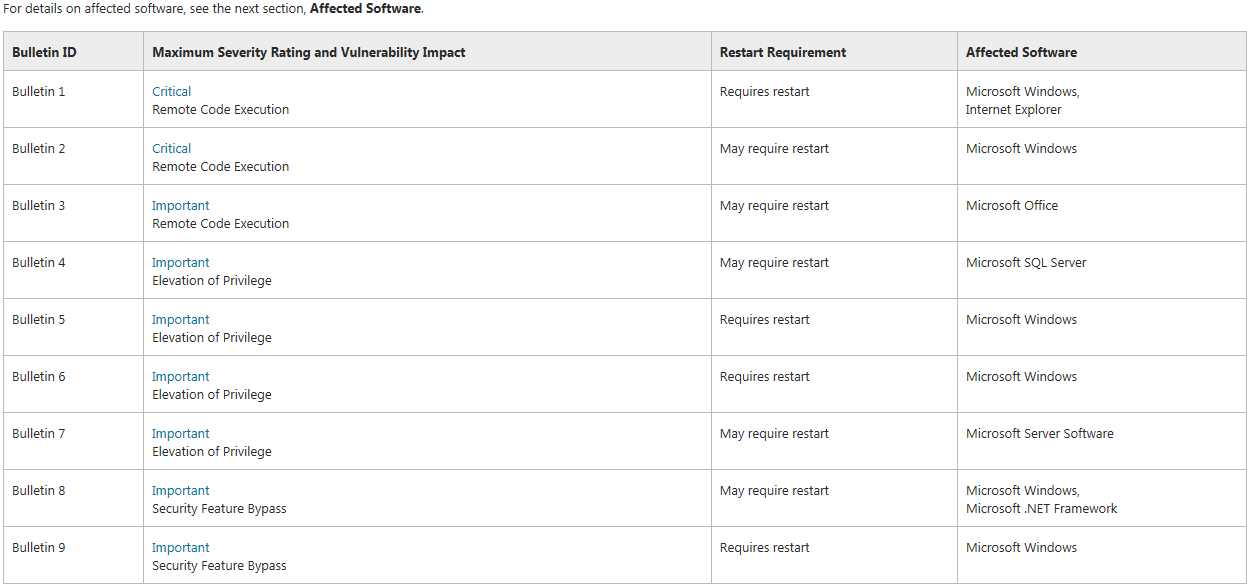
In the case of Microsoft, the company released a total of nine security bulletins to patch 37 bugs. Included in that number are critical fixes for Internet Explorer and Windows. The Internet Explorer bulletin addresses a total of 26 vulnerabilities, including one that was publicly disclosed. The most severe of the issues can be exploited to allow remote code execution when a user views a specially-crafted webpage using IE.
"IT’s first priority should be the critical, cumulative update for IE," blogged Russ Ernst, director of product management at Lumension. "MS14-051 includes 25 CVEs for all supported versions of the browser. All are privately disclosed with the exception of one, CVE-2014-2819, which was publicly disclosed just last week at Black Hat. It allows an attacker to bypass the application sandbox and elevate privilege but it must be combined with another remote code execution vulnerability to ultimately be successful."
The second critical update is aimed at Windows.
"The vulnerability could allow remote code execution if a user opens a specially crafted Microsoft Office file that invokes Windows Media Center resources," Microsoft explained in its bulletin summary. "An attacker who successfully exploited this vulnerability could gain the same user rights as the current user. Customers whose accounts are configured to have fewer user rights on the system could be less impacted than those who operate with administrative user rights."
Outside of those two, Microsoft's other bulletins were 'important', and impact Microsoft OneNote, SQL Server, Windows, Microsoft Server Software and the .NET framework.
In addition to the Microsoft updates, Adobe Systems released patches for Adobe Flash Player, Adobe Reader and Adobe Acrobat. While the Adobe Flash Player bugs are not known to be under attack, the company said it is aware of evidence of an exploit in the wild being used against Adobe Reader users on Windows in targeted attacks. According to Adobe, the Reader and Acrobat updates address a vulnerability that could enable an attacker to circumvent sandbox protection on the Windows platform. Users on Mac OS X are not affected.
Source/ SecurityWeek/ http://www.securityweek.com/microsoft-fixes-critical-vulnerabilities-internet-explorer-windows
(Microsoft Fixes Critical Vulnerabilities in Internet Explorer, Windows )
By Brian Prince on August 12, 2014 Microsoft and Adobe released a set of patches today to fix critical vulnerabilities in their products.
In the case of Microsoft, the company released a total of nine security bulletins to patch 37 bugs. Included in that number are critical fixes for Internet Explorer and Windows. The Internet Explorer bulletin addresses a total of 26 vulnerabilities, including one that was publicly disclosed. The most severe of the issues can be exploited to allow remote code execution when a user views a specially-crafted webpage using IE.
"IT’s first priority should be the critical, cumulative update for IE," blogged Russ Ernst, director of product management at Lumension. "MS14-051 includes 25 CVEs for all supported versions of the browser. All are privately disclosed with the exception of one, CVE-2014-2819, which was publicly disclosed just last week at Black Hat. It allows an attacker to bypass the application sandbox and elevate privilege but it must be combined with another remote code execution vulnerability to ultimately be successful."
The second critical update is aimed at Windows.
"The vulnerability could allow remote code execution if a user opens a specially crafted Microsoft Office file that invokes Windows Media Center resources," Microsoft explained in its bulletin summary. "An attacker who successfully exploited this vulnerability could gain the same user rights as the current user. Customers whose accounts are configured to have fewer user rights on the system could be less impacted than those who operate with administrative user rights."
Outside of those two, Microsoft's other bulletins were 'important', and impact Microsoft OneNote, SQL Server, Windows, Microsoft Server Software and the .NET framework.
In addition to the Microsoft updates, Adobe Systems released patches for Adobe Flash Player, Adobe Reader and Adobe Acrobat. While the Adobe Flash Player bugs are not known to be under attack, the company said it is aware of evidence of an exploit in the wild being used against Adobe Reader users on Windows in targeted attacks. According to Adobe, the Reader and Acrobat updates address a vulnerability that could enable an attacker to circumvent sandbox protection on the Windows platform. Users on Mac OS X are not affected.
Source/ SecurityWeek/ http://www.securityweek.com/microsoft-fixes-critical-vulnerabilities-internet-explorer-windows
Reply
Login to the community
No account yet? Create an account
Enter your username or e-mail address. We'll send you an e-mail with instructions to reset your password.