New Man-in-the-Middle attacks leveraging rogue DNS
PhishLabs has observed a new wave of "Man-in-the-Middle" (MitM) attacks targeting users of online banking and social media. Customers of more than 70 different financial institutions are being targeted.
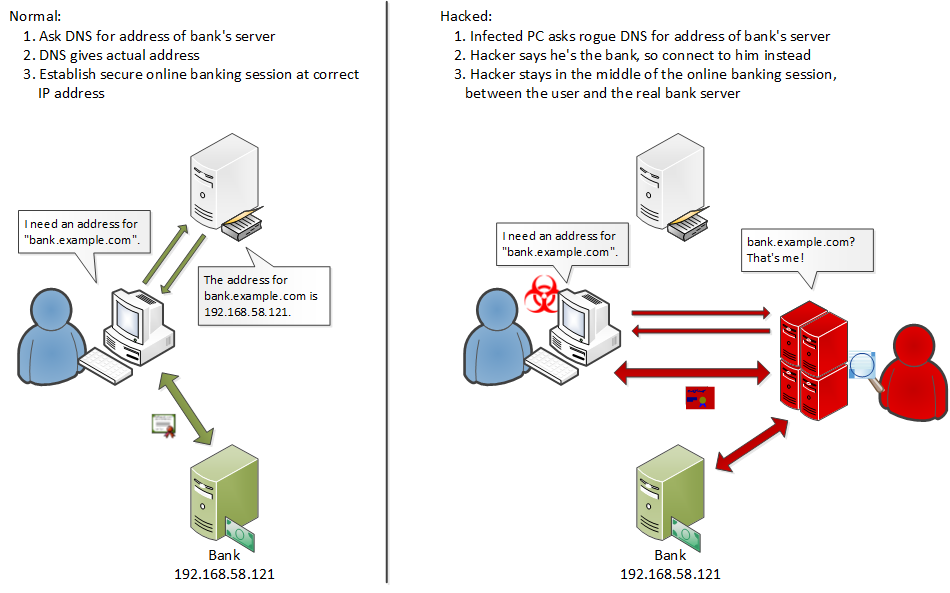
In these attacks, hackers use spam to deliver malware that changes DNS settings and installs a rogue Certificate Authority (CA). The DNS changes point to the hacker's clandestine DNS name server so that users are directed to proxy servers instead of legitimate sites. Based on the CA, the user's PC trusts the attacker’s proxy servers and provides no indication that an attack is taking place. The browser displays the proper website name and displays the familiar security icon to indicate a trusted, secure connection.
The hacker's proxy sits between the authorized user and the real website, capturing login credentials and injecting code into the browsing session. This allows the hacker to take total control of the user's account and carry out unauthorized banking transactions as well as other actions.
Full Article
Be the first to reply!
Reply
Login to the community
No account yet? Create an account
Enter your username or e-mail address. We'll send you an e-mail with instructions to reset your password.