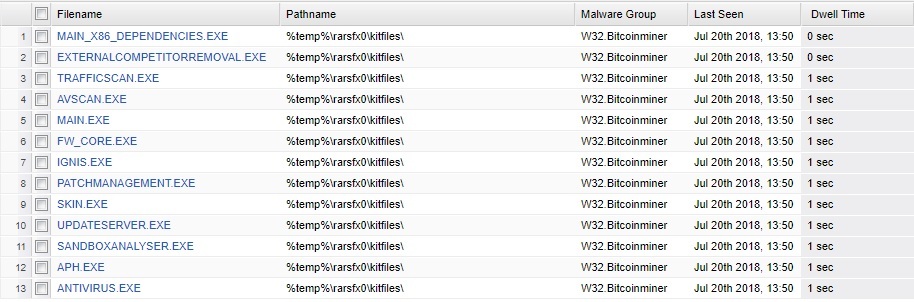
We have an infection currently spreading through our network. New endpoints are popping up on the SecureAnywhere console every few minutes as infected. Some are 'protected', others are 'need attention'. The infection is reported as W32.BitCoinMiner. The file list is shown below.
I need to determine
a. The point of entry - which computer introduced this and how. Was it via the web? local usb device? etc.
b. How the infection is able to spread. So far it has affected two AD sites, spanning two IP subnets. It has not spread to any servers yet.
Does anyone have any tips on how best to understand and investigate the two points above?
Many thanks
Michael.
Best answer by DDIT
View original