I recently bought an HP laptop with Windows 10 Home installed on it, previously using Windows 7 and WRSA on othr PCs.
I installed WRSA Antivirus on the new laptop and the Windows 10 firewall is switched on, also the WRSA firewall is switched on.
I am a long-time WRSA user and recall that the WRSA firewall works in a complementary way on top of the Windows firewall, so no problems so far....
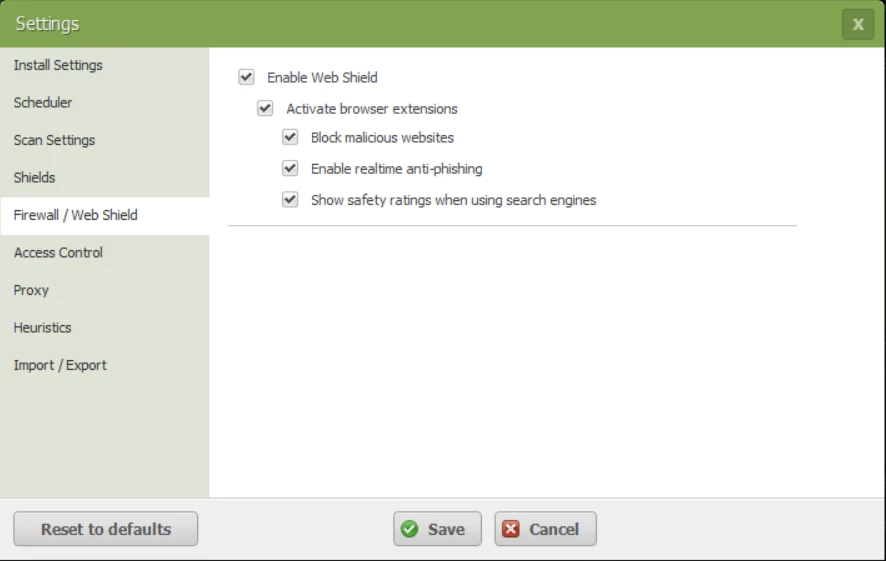
In advanced settings, under Firewall / Webshield there appear only webshield options, the Firewall options are completely blank. Is this normal on Windows 10 ?
I previously used WRSA Complete so I thought that restriction might be due to version differences as well?
Screenshot attached. Appreciate a quick answer please, need to go travelling soon and would like to increase the level of firewall protection to alert when new unknown processes start, not just when WRSA thinks I am infected..
Page 2 / 2
Thanks, Nemo, for precisely emphasising the point I have been trying to make...that the WSA approach is not a risky one but in fact a very sane approach to the problem...leave the inactive & therefire benign stuff, until it tries to activate, and concentrate on those nasties that are trying to do...well, the nasty stuff to one's system. 😃@ wrote:
Many thanks Dan for your input. Assuming all samples behave similarly, then we it looks as though we are quite safe - and have been all along! :D
Thanks Dan. Can you explain though the purpose of a manual scan of a file? If I download several emails with almost-certain malware attachments and during the download they don't get identified by WRSA as being anything to worry about, well, I can understand the philosophy that they are not active and to leave them.
But during download is it actually detecting and comparing with the remote online database, or just ignoring the download? If detecting but then leaving until active, why not just quaranteen and get it off the PC as soon as possible rather than taking a risk later? If leaving it because it does not actually scan the download, then OK, I can understand it will be left alone by default.
Second scenario is manual scanning. If I purposefully right click over the downloaded suspected malware files and request a manual scan by Webroot then it must surely be comparing the signature against the online database - it's own or Virustotal for example. So now it has been asked, and now knows there is a malicious payload, so why not quaranteen or remove immediately? Otherwise if left after the scan, it is giving a false impression that the file is legitimate.
What if I don't open that file (therefore WRSA will not get the chance to jumpt on it) but instead pass it on to someone else thinking it's not an infected file and the other user is not a Webroot user? Their AV will alert them to a malicious file probably, before they even try opening it. I will have sent them a malicious file and risked their system and data integrity!
So under the philisophy of Webroot monitoring file behaviour and then only acting, what is the actual purpose of having a manual scan ability which does not actually alert the user to trojan downloaders, macro virus and other nasties? In the past 2 weeks I have tested more than 20 such malware attachments and WRSA just alerted me on one, and I think that was on actual download not manual scan. The same sample had Windows Defender catch all but 2 on download and then on manual scan those 2 were dealt with.
When I ran Windows 7 this kind of feature was resolved because I ran MS Security Essentials and WRSA together but under Windows 10 it is not possible to run Defender and WRSA. Although yesterday I read on these forums that there is a registry hack to allow this, so I am trying it out now, but I am not sure if WRSA will recognise WD as the "primary" AV and allow it to do it's thing when spotting malware and only act if WD fails, or else it will fight with WD to own the malware and deal with it!
But during download is it actually detecting and comparing with the remote online database, or just ignoring the download? If detecting but then leaving until active, why not just quaranteen and get it off the PC as soon as possible rather than taking a risk later? If leaving it because it does not actually scan the download, then OK, I can understand it will be left alone by default.
Second scenario is manual scanning. If I purposefully right click over the downloaded suspected malware files and request a manual scan by Webroot then it must surely be comparing the signature against the online database - it's own or Virustotal for example. So now it has been asked, and now knows there is a malicious payload, so why not quaranteen or remove immediately? Otherwise if left after the scan, it is giving a false impression that the file is legitimate.
What if I don't open that file (therefore WRSA will not get the chance to jumpt on it) but instead pass it on to someone else thinking it's not an infected file and the other user is not a Webroot user? Their AV will alert them to a malicious file probably, before they even try opening it. I will have sent them a malicious file and risked their system and data integrity!
So under the philisophy of Webroot monitoring file behaviour and then only acting, what is the actual purpose of having a manual scan ability which does not actually alert the user to trojan downloaders, macro virus and other nasties? In the past 2 weeks I have tested more than 20 such malware attachments and WRSA just alerted me on one, and I think that was on actual download not manual scan. The same sample had Windows Defender catch all but 2 on download and then on manual scan those 2 were dealt with.
When I ran Windows 7 this kind of feature was resolved because I ran MS Security Essentials and WRSA together but under Windows 10 it is not possible to run Defender and WRSA. Although yesterday I read on these forums that there is a registry hack to allow this, so I am trying it out now, but I am not sure if WRSA will recognise WD as the "primary" AV and allow it to do it's thing when spotting malware and only act if WD fails, or else it will fight with WD to own the malware and deal with it!
@ wrote:
Thanks Dan. Can you explain though the purpose of a manual scan of a file? If I download several emails with almost-certain malware attachments and during the download they don't get identified by WRSA as being anything to worry about, well, I can understand the philosophy that they are not active and to leave them.
But during download is it actually detecting and comparing with the remote online database, or just ignoring the download? If detecting but then leaving until active, why not just quaranteen and get it off the PC as soon as possible rather than taking a risk later? If leaving it because it does not actually scan the download, then OK, I can understand it will be left alone by default.
Second scenario is manual scanning. If I purposefully right click over the downloaded suspected malware files and request a manual scan by Webroot then it must surely be comparing the signature against the online database - it's own or Virustotal for example. So now it has been asked, and now knows there is a malicious payload, so why not quaranteen or remove immediately? Otherwise if left after the scan, it is giving a false impression that the file is legitimate.
What if I don't open that file (therefore WRSA will not get the chance to jumpt on it) but instead pass it on to someone else thinking it's not an infected file and the other user is not a Webroot user? Their AV will alert them to a malicious file probably, before they even try opening it. I will have sent them a malicious file and risked their system and data integrity!
So under the philisophy of Webroot monitoring file behaviour and then only acting, what is the actual purpose of having a manual scan ability which does not actually alert the user to trojan downloaders, macro virus and other nasties? In the past 2 weeks I have tested more than 20 such malware attachments and WRSA just alerted me on one, and I think that was on actual download not manual scan. The same sample had Windows Defender catch all but 2 on download and then on manual scan those 2 were dealt with.
When I ran Windows 7 this kind of feature was resolved because I ran MS Security Essentials and WRSA together but under Windows 10 it is not possible to run Defender and WRSA. Although yesterday I read on these forums that there is a registry hack to allow this, so I am trying it out now, but I am not sure if WRSA will recognise WD as the "primary" AV and allow it to do it's thing when spotting malware and only act if WD fails, or else it will fight with WD to own the malware and deal with it!
In the examples you have given, the attachments have been non-executable files containing exploits that will download and run an executable file when opened, at which point the malicious payload would be detected. For the most part, we focus on the actual executables, which is why those files would not be detected when downloaded or manually scanning the files. If you were to download an attachment that was actually an executable file, it would be detected on download or manual scan.
While it is possible that you could download one of these attachements and send it to someone else, you did mention in an earlier post that you downloaded those attachments from your spam folder, so I don't think that you would actually go into your spam folder, download a suspicious attachement and send it to someone else.
-Dan
Dan, thanks for clarifying.@ wrote:
@ ,
In the examples you have given, the attachments have been non-executable files containing exploits that will download and run an executable file when opened, at which point the malicious payload would be detected. For the most part, we focus on the actual executables, which is why those files would not be detected when downloaded or manually scanning the files. If you were to download an attachment that was actually an executable file, it would be detected on download or manual scan.
While it is possible that you could download one of these attachements and send it to someone else, you did mention in an earlier post that you downloaded those attachments from your spam folder, so I don't think that you would actually go into your spam folder, download a suspicious attachement and send it to someone else.
-Dan
I had assumed that attachments detected as Trojans by WRSA and other AVs would be considered by WRSA as capable of executing a malware process directly or indirectly, hence cause for WRSA to act immediately from the get-go.
The scenario that I painted, I would not actually have forwarded such an email myself, but was using myself as an example of someone such a business professional who receives an invoice or Fedex delivery note by email and then forwards it to an admin person to administer. That admin person might not be in the same office therefore not have WRSA, they could be outsourced and have another AV. So in other words, my point is that if WRSA knows that it has a Trojan or other malware not yet executed, then the owner of the PC may pass on the file unaware that it is malicious. WRSA could have already taken action which Defender and many other AVs would have already taken to neutralise the threat.
I don't want to change AVs, I like WRSA but was really surprised to experience so many malicious files (a sample of more than 20) being passed by WRSA as being OK at download and manual scan. AT the time of download or manual scan WRSA is, I guess, already looking up that file online and so it can check the signature and know it is suspicious. So why not quaranteen it then, or at least put a flag on it to warn the user? From the user's point of view that file just received a clean bill of health not once but TWICE by WRSA (at download and manual scan) when in fact it was widely known as a malicious file. In other words, by twice giving the OK status to a file, WRSA is mis-representing that file as a legitimate file and that file may continue through the user's workflow and do a lot of damage elewhere.
Surely does not add bloat to WRSA to online lookup a file even on Virustotal and know it's a suspect and quaranteen it imediately?
In the meantime that's exactly why Webroot should allow people like me and quite a few others who used WRSA on Windows7 together with MS Security Essentials which sweeps up all these obvious Trojans and just leaves WRSA for the more elucid malware, to now do the same on Windows 10, but as you will be aware, WD and WRSA cannot run together on Windows 10.
I realise I raise a few issues, but I assure you that main aim is to have an even better WRSA that we have now whilst also raising legitimately serious issues from the real world of the user. I use WRSA on my business PCs and I am explaining these real world scenarious from real experience of how people work, it's not a theoretical discussion.
Dan, thanks for clarifying.@ wrote:
I had assumed that attachments detected as Trojans by WRSA and other AVs would be considered by WRSA as capable of executing a malware process directly or indirectly, hence cause for WRSA to act immediately from the get-go.
The scenario that I painted, I would not actually have forwarded such an email myself, but was using myself as an example of someone such a business professional who receives an invoice or Fedex delivery note by email and then forwards it to an admin person to administer. That admin person might not be in the same office therefore not have WRSA, they could be outsourced and have another AV. So in other words, my point is that if WRSA knows that it has a Trojan or other malware not yet executed, then the owner of the PC may pass on the file unaware that it is malicious. WRSA could have already taken action which Defender and many other AVs would have already taken to neutralise the threat.
I don't want to change AVs, I like WRSA but was really surprised to experience so many malicious files (a sample of more than 20) being passed by WRSA as being OK at download and manual scan. AT the time of download or manual scan WRSA is, I guess, already looking up that file online and so it can check the signature and know it is suspicious. So why not quaranteen it then, or at least put a flag on it to warn the user? From the user's point of view that file just received a clean bill of health not once but TWICE by WRSA (at download and manual scan) when in fact it was widely known as a malicious file. In other words, by twice giving the OK status to a file, WRSA is mis-representing that file as a legitimate file and that file may continue through the user's workflow and do a lot of damage elewhere.
Surely does not add bloat to WRSA to online lookup a file even on Virustotal and know it's a suspect and quaranteen it imediately?
In the meantime that's exactly why Webroot should allow people like me and quite a few others who used WRSA on Windows7 together with MS Security Essentials which sweeps up all these obvious Trojans and just leaves WRSA for the more elucid malware, to now do the same on Windows 10, but as you will be aware, WD and WRSA cannot run together on Windows 10.
I realise I raise a few issues, but I assure you that main aim is to have an even better WRSA that we have now whilst also raising legitimately serious issues from the real world of the user. I use WRSA on my business PCs and I am explaining these real world scenarious from real experience of how people work, it's not a theoretical discussion.
But you can run WD with WSA but why would you want to?
https://community.webroot.com/t5/Webroot-SecureAnywhere-Complete/What-s-the-difference-between-the-new-Windows-Defender-and/ta-p/13852
https://community.webroot.com/t5/Webroot-SecureAnywhere-Antivirus/How-to-Run-WSA-alongside-Windows-Defender-on-Windows-8-Windows-8/ta-p/23058
Thanks,
Daniel
Hi Daniel, thanks for the suggestion, but I am going around full circle, let me explain...@ wrote:
But you can run WD with WSA but why would you want to?
https://community.webroot.com/t5/Webroot-SecureAnywhere-Complete/What-s-the-difference-between-the-new-Windows-Defender-and/ta-p/13852
https://community.webroot.com/t5/Webroot-SecureAnywhere-Antivirus/How-to-Run-WSA-alongside-Windows-Defender-on-Windows-8-Windows-8/ta-p/23058
Thanks,
Daniel
I want to use WRSA exclusively, but I see there are issues, above, about WRSA not dealing with at least 20 recent Trojans in my sample during a) download nor b) upon manual scan request. There was no warning. Now you guys, will say the malware is not active, but I say, if WRSA knows there is a Trojan in the file then quaranteen it immediately, not wait, because in the meantime someone can pass that file on to another person thinking it's OK. Otherwise, Webroot should not be offering a manual scan option and giving users a false sense of security, period. Defender and other AVs identify and quaranteen or delete the Trojan immediately.
So my potential solution is to use Defender and WRSA side by side. As you show, there is a registry hack for that, and I have been using it for a couple of days now. But, in Windows 7, WRSA has logic to allow MS Security Essentials to first deal with any malware and only if MSE does not deal with it, WRSA then jumps in. But, in Windows 10, WRSA is not expecting to see WD switched on because MS don't allow it. So my question was on another thread and still awaiting an answer, with this registry tweak on Windows 10 to allow WD and WRSA run together, will WRSA recognise WD actions and wait for it, or else will WRSA wrestle with WD over a piece of malware they both recognise, unlike in Windows 7 ?
In summary, my preference is to keep WRSA and see it improved handling of such Trojans. In the meantime I want to use on Windows 10 WRSA and WD together, but I am concerned they might fight over the same malware unlike in Windows 7.
Hope this clarifies my concerns and I hope someone can give an informed answer concerning the way that WRSA works alongside WD on Windows 10 when it's not expecting to do so.
Cheers.
Hi cavehomme
I am afraid that you are getting yourself in a lather for nothing. WSA has been built, from the ground upwards, to be compliant to other security solutions that might run with it...as far as I am aware it is one of the few if not the only security app to do so by design...and as I understand it WSA lets the other security app have a first go at protection but watches what occurs very carefully and if the other application lets anything through WSA springs into action to deal with the 'miss'.
Personally, I would not worry about the "...they might fight over the same malware unlike in Windows 7".
Just my two pence worth...for what it is worth, and hopefully DanP will confirm that. ;)
Regards, Baldrick
I am afraid that you are getting yourself in a lather for nothing. WSA has been built, from the ground upwards, to be compliant to other security solutions that might run with it...as far as I am aware it is one of the few if not the only security app to do so by design...and as I understand it WSA lets the other security app have a first go at protection but watches what occurs very carefully and if the other application lets anything through WSA springs into action to deal with the 'miss'.
Personally, I would not worry about the "...they might fight over the same malware unlike in Windows 7".
Just my two pence worth...for what it is worth, and hopefully DanP will confirm that. ;)
Regards, Baldrick
Overriding Windows functionality like that is not something we can recommend or support, but it should not cause issues if you choose to do so.@ wrote:
Hi cavehomme
I am afraid that you are getting yourself in a lather for nothing. WSA has been built, from the ground upwards, to be compliant to other security solutions that might run with it...as far as I am aware it is one of the few if not the only security app to do so by design...and as I understand it WSA lets the other security app have a first go at protection but watches what occurs very carefully and if the other application lets anything through WSA springs into action to deal with the 'miss'.
Personally, I would not worry about the "...they might fight over the same malware unlike in Windows 7".
Just my two pence worth...for what it is worth, and hopefully DanP will confirm that. ;)
Regards, Baldrick
-Dan
Thanks Baldrick and thanks Dan.
I'm not worked up in a lather / froth, I hope, just scratching my head trying to understand how my favourite AV works in detail ;)
I am also applying logic, that if a software is designed to work one way, even from the ground up, then it might not work the exact same way in a different environment (e.g. Win10 vs Win 7) due to design considerations for two different environments.
But now I am more comfortable with your answers, thanks.
That said, I still don't understand when WRSA recognises a Trojan via it's scan and lookup, it simply leaves it there untouched and unflagged, for "ignorant" users to assume it's OK and possibly pass that malicious file on to another person in the workflow who does not use somethng as advanced as WRSA.
Bottom line for me as a designer would be, once you suspect something may be malicious then for goodness sake deal with it immediately, there and then, not wait until it becomes active. :@
I'm not worked up in a lather / froth, I hope, just scratching my head trying to understand how my favourite AV works in detail ;)
I am also applying logic, that if a software is designed to work one way, even from the ground up, then it might not work the exact same way in a different environment (e.g. Win10 vs Win 7) due to design considerations for two different environments.
But now I am more comfortable with your answers, thanks.
That said, I still don't understand when WRSA recognises a Trojan via it's scan and lookup, it simply leaves it there untouched and unflagged, for "ignorant" users to assume it's OK and possibly pass that malicious file on to another person in the workflow who does not use somethng as advanced as WRSA.
Bottom line for me as a designer would be, once you suspect something may be malicious then for goodness sake deal with it immediately, there and then, not wait until it becomes active. :@
Hi cavehomme
Look, it is really simple in my book...the designer of WSA designed it to work in a certain way, based on certain permises...and work it does based on that design...as such I have chosen to trust in that design and its execution...and I leave it at that.
As far as I am concerned that is all good for me/I am happy with that.
You are free to express your views as you see fit and they are as valid as anyone elses...as they are yours...just don't expect anyone to act on them any time soon. That is Webroot's choice in the matter...if they want to they will and if they don't they won't.
Regards, Baldrick
Look, it is really simple in my book...the designer of WSA designed it to work in a certain way, based on certain permises...and work it does based on that design...as such I have chosen to trust in that design and its execution...and I leave it at that.
As far as I am concerned that is all good for me/I am happy with that.
You are free to express your views as you see fit and they are as valid as anyone elses...as they are yours...just don't expect anyone to act on them any time soon. That is Webroot's choice in the matter...if they want to they will and if they don't they won't.
Regards, Baldrick
Userlevel 3
I hate to throw any more wood on this fire but I have to say...
I chose WEBROOT because it appears to do its job while using the least amount of system resources. Yes, I could get a product that scans all files, every bit sent or received via Ethernet, wifi, serial cable etc... but having had a couple of those type products before, I found them to be too intrusive on my day to day activities. They took my custom built I7, 16gig, 1TB SSD machine and turned it into a 1990's era Celeron machine!
I personally believe that security starts with the user. If you don't know where the email came from, or who gave you the file via whatever media, DON'T OPEN IT. On the machines I administered (Which happened to be process control stations in industry) I disabled all USB ports, and any removable media. I also made sure that users were not allowed administrator privileges. This carries over to my personal machines as well.
One last thing, I know of several people that have joined various peer to peer networks. These people are usually first in line to get hit with the various forms of Malware and Virus software that is circulating the net today. I wonder why?? (Sarcasm)
My point is, use a quality product (Webroot) for AV, make my your router / gateway has a quality firewall, then let the MS firewall handle what slips though. And last but not least use your head, and keep plenty of backups.
I chose WEBROOT because it appears to do its job while using the least amount of system resources. Yes, I could get a product that scans all files, every bit sent or received via Ethernet, wifi, serial cable etc... but having had a couple of those type products before, I found them to be too intrusive on my day to day activities. They took my custom built I7, 16gig, 1TB SSD machine and turned it into a 1990's era Celeron machine!
I personally believe that security starts with the user. If you don't know where the email came from, or who gave you the file via whatever media, DON'T OPEN IT. On the machines I administered (Which happened to be process control stations in industry) I disabled all USB ports, and any removable media. I also made sure that users were not allowed administrator privileges. This carries over to my personal machines as well.
One last thing, I know of several people that have joined various peer to peer networks. These people are usually first in line to get hit with the various forms of Malware and Virus software that is circulating the net today. I wonder why?? (Sarcasm)
My point is, use a quality product (Webroot) for AV, make my your router / gateway has a quality firewall, then let the MS firewall handle what slips though. And last but not least use your head, and keep plenty of backups.
Hi gahelm
Would not disagree with what you say and it all seems to be common sense advice...having said that if everyone headed common sense advice then the malware miscreants out there would have a much harder time of it.
Regards, Baldrick
Would not disagree with what you say and it all seems to be common sense advice...having said that if everyone headed common sense advice then the malware miscreants out there would have a much harder time of it.
Regards, Baldrick
Page 2 / 2
Reply
Login to the community
No account yet? Create an account
Enter your username or e-mail address. We'll send you an e-mail with instructions to reset your password.