I tried to submit this via a support ticket but it doesn't allow me to enter my password.
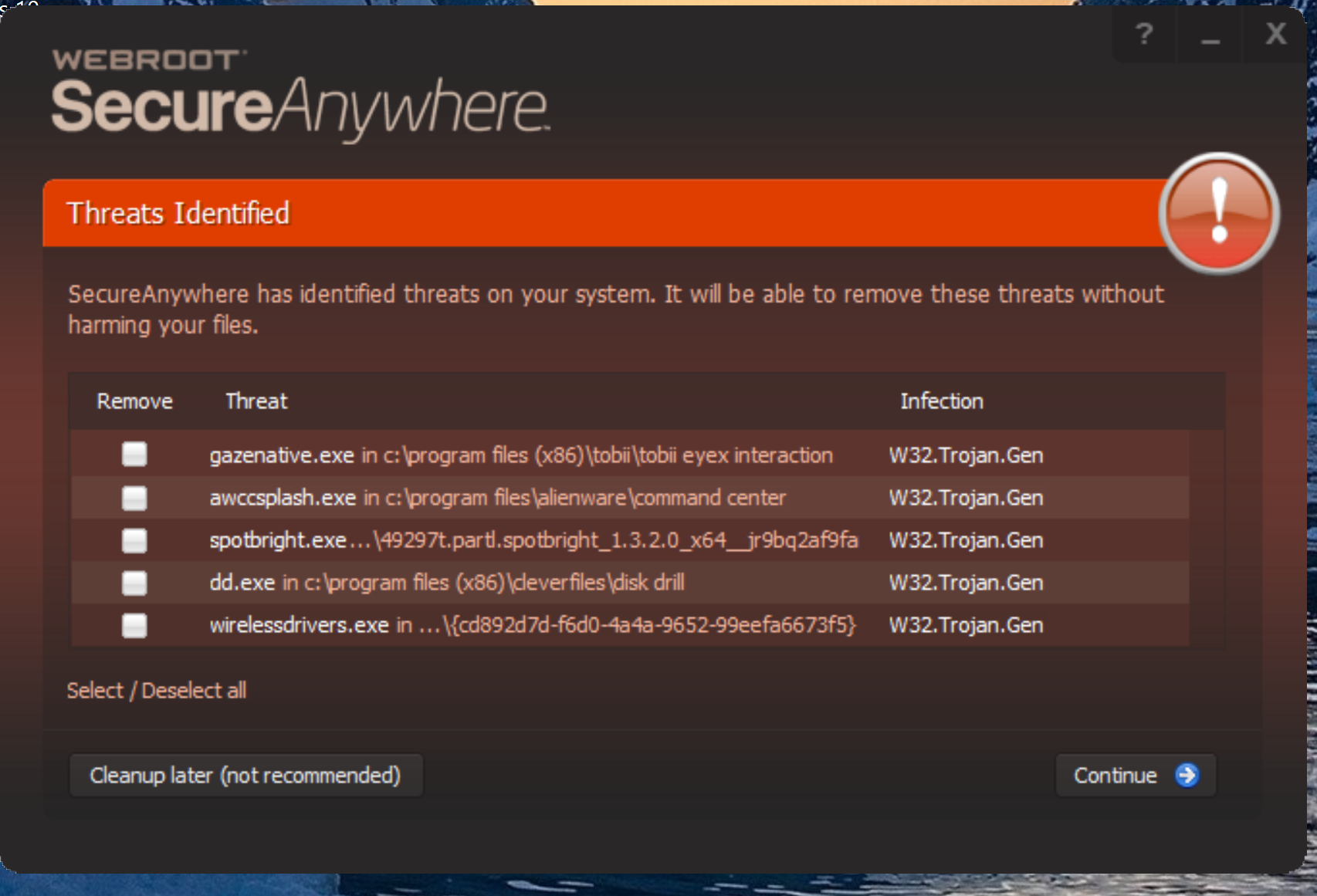
I uploaded one of the files, spriter.exe, to virustotal.com and it is only hitting on webroot so I'm thinking false positives. Here is scan info from my log:
Mon 2017-04-24 16:03:51.0632 Performing cleanup entry: 8
Mon 2017-04-24 16:03:51.0927 End passive write scan (6 file(s))
Mon 2017-04-24 16:03:54.0036 Scan Started: [ID: 406 - Flags: 1575/128]
Mon 2017-04-24 16:04:35.0520 Infection detected: c:program filescanonprint studio procnpspapp.exe [MD5: CD90CC76609BEDB3C96D02A222840308] [3/00091411] [W32.Trojan.Gen]
Mon 2017-04-24 16:04:35.0520 Infection detected: e:steamlibrarysteamappscommoncommand modern air naval operationscommand.exe [MD5: 899C8F65A68D4338D6A0DA097A3EDDB1] [3/10081001] [W32.Trojan.Gen]
Mon 2017-04-24 16:04:40.0929 Infection detected: c:usersandroappdata
oaminggamemaker-studioyycwindowsuapexex86winuaprunner.exe [MD5: 20FBBF64F5E1DF867E0005AF031D6B19] [3/00080011] [W32.Trojan.Gen]
Mon 2017-04-24 16:04:50.0058 Infection detected: e:steamlibrarysteamappscommonattlezone 98 reduxattlezone98redux.exe [MD5: 0441A9C1B53AFB8FB5FF69F1AA03D9FD] [3/08080001] [W32.Trojan.Gen]
Mon 2017-04-24 16:04:56.0982 Infection detected: e:steamlibrarysteamappscommonspriterspriter.exe [MD5: 57B5433954076D20426A229E1BDC8D22] [3/00000001] [W32.Trojan.Gen]
Mon 2017-04-24 16:04:56.0982 Infection detected: e:steamlibrarysteamappscommoncommand modern air naval operationsgamemenu_cmanoautorun.exe [MD5: 5CEAC3EC1728E0C2926E3AD58A41D97C] [3/10081001] [W32.Trojan.Gen]
Mon 2017-04-24 16:04:59.0890 Infection detected: c:usersandroappdata
oaminggamemaker-studioyycwindowsuapexex64winuaprunner.exe [MD5: 9A0178B18C9DCE6589C8E6D1AC680207] [3/00090011] [W32.Trojan.Gen]
Mon 2017-04-24 16:05:00.0437 Scan Results: Files Scanned: 17929, Duration: 1m 6s, Malicious Files: 7
Mon 2017-04-24 16:05:00.0594 Scan Finished: [ID: 406 - Seq: 191448274]
Page 1 / 2
i'm getting Brutal Doom 64, one of my games and EVERYTHING involving SteamVR
Userlevel 7
Thanks, @
Our Team is aware of the rule causing False Positives and is actively working now to resolve. Please stay tuned for updates.
Our Team is aware of the rule causing False Positives and is actively working now to resolve. Please stay tuned for updates.
Getting tyhe same re. about 25 .exes that I know are clean, and in fact have been on my system for some weeks now...so something gone a bit funny in the Cloud...I reckon.
Baldrick
Baldrick
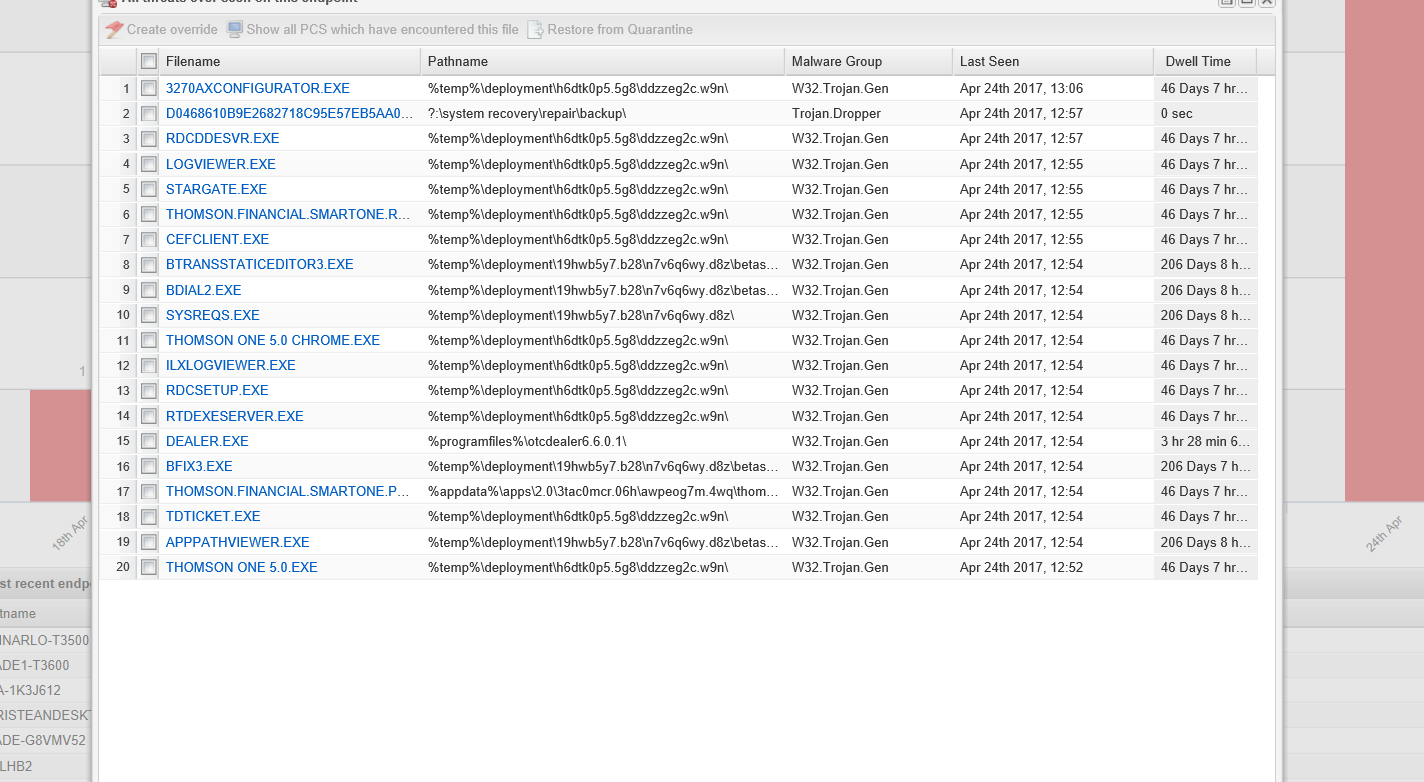
Brought down one of my servers with Sage Businessworks installed. I was not able to restore from quarantine via web panel.. or either I didn't wait long enough. I ended up having to set the Endpoint as unmanaged and restore directly from the GUI on the server.
How long should have the restore have taken and I hope this gets fixed VERY quickly before it flags anymore of my servers as malicious.
What is everyone's recommendation about removing server files? Do you have it set to automatically resolve or just send the alert so that you can determine what to do with the file?
How long should have the restore have taken and I hope this gets fixed VERY quickly before it flags anymore of my servers as malicious.
What is everyone's recommendation about removing server files? Do you have it set to automatically resolve or just send the alert so that you can determine what to do with the file?
 +1
+1
i can imagine someone on break playing something like Rocket League and they get kicked off and Webroot locking them off the game
Same here. I was up to 83 false positives in c:windowssystem32 before I just gave up and disabled Webroot. Everything I submitted to VirusTotal showed up with old hashes and 0 hits, but re-analysing the exact same file showed only 1 new hit, which was Webroot.
I'm not sure what all it screwed up but one of the exes was needed to raise admin privileges. It finally had multiple scans going at once and just locked my PC for 20 minutes. That's when I just gave up, powered on, and disabled it. I have this deployed on hundreds of clients and servers at my company so I hope this doesn't wipe us out today.
It appears some update today has screwed things up badly.
Windows 10 64bit Faster insider ring.
I'm not sure what all it screwed up but one of the exes was needed to raise admin privileges. It finally had multiple scans going at once and just locked my PC for 20 minutes. That's when I just gave up, powered on, and disabled it. I have this deployed on hundreds of clients and servers at my company so I hope this doesn't wipe us out today.
It appears some update today has screwed things up badly.
Windows 10 64bit Faster insider ring.
Or a multi-million dollar company trying to conduct business and not able to because it has flagged server applications as malicious and quarantined them. I would have much rathered it be Rocket League not opening.
FYI This is taking out all of the MSPs. Specifically we are losing almost all .EXE files across all of our clients.
It is also hitting our management tools so this has the potential to become a huge labor issue.
Do you have any recommended policy settings that we can setup as a new policy to temporarily put a halt to them?
It is also hitting our management tools so this has the potential to become a huge labor issue.
Do you have any recommended policy settings that we can setup as a new policy to temporarily put a halt to them?
Userlevel 1
We are in teh same boat here...tons of false positives today. I has set it not to resolve by deletion..but who knows how long that will take. So far removed everything from updaters to database management tools. This is pretty awful. Really hope the restore from quarantine works. Noticed in the logs webroot also deletes registry and any associated config files as well for delete applications.
from the looks it's ALL OVER....random....i hope it doesnt....i dont have money to move to someone else ><
Hey everyone, we are aware of a rule change causing technical issues. Our team is working to restore functionality. We will provide updates as info becomes available.
Thank you for your patience and sticking with us while we troubleshoot this issue.
More to come as soon as we have it.
Thank you for your patience and sticking with us while we troubleshoot this issue.
More to come as soon as we have it.
This is brutal. It's detecting all kinds of files and causing our clients major grief. It's affect about eight of our managed clients.
Thanks for the update, freydrew, much obliged.
I am sure that the Support & Development Teams are working flat out and will have the issue sorted very shortly...as they usually do.
Regards, Baldrick
I am sure that the Support & Development Teams are working flat out and will have the issue sorted very shortly...as they usually do.
Regards, Baldrick
Our helpdesk blew up this afternoon. Please revert whatever change was made today
Userlevel 1
Is there a way to get all the false positives that have deleted automatically? This is going to be a nightmare for us otherwise.
I have turned off scheduled scan and real-time shield until a fix has been pushed out. It won't undo any damage already done but will hopefully help mitigate further false positives.
the SteamVR stuff i can recover and the small apps...this could of been a WHOLE LOT WORSE to me ;w; i kinda feel bad to the ones that get like EVERYTHING paned
Hopefully we can get notified when it is fixed. We'll uninstall Webroot until a fix is available since we've never seen any way to just disable it (without reactivating on reboot).
Add Altium Designer (dxp.exe) to the list of false positives. WR deleted the .exe and now won't allow re-download or re-installation of the software. Not good.
this also happened to me...it also is preventing me AS THE ADMIN to even put anything thats flagged in....saying i dont have permission
Userlevel 1
Trying to restore files from quarantine, I tried from the web console and refreshed config, no go yet. Also tried to restore from the machine itself but says it is managed by the web console. Do you have a recommended method to restore files deleted by this issue? I have locked my door and hiding from the users until I have an answer.
We are finding at least a 20 minute lag time on the restores. I would not uninstall since you may lose your quarantine items...
Webroot -
Please at least provide what we should be making the policy set to to avoid the issue...
Steve
Please at least provide what we should be making the policy set to to avoid the issue...
Steve
Page 1 / 2
Reply
Login to the community
No account yet? Create an account
Enter your username or e-mail address. We'll send you an e-mail with instructions to reset your password.