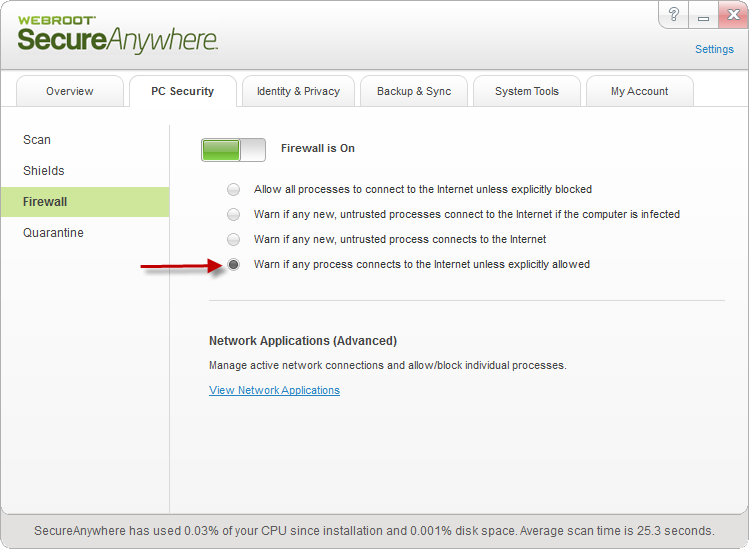
Having the firewall setup "Warn if any process connects to the internet unless explicitly allowed" and wanted to check how it works ending up quite surprised in the end ...
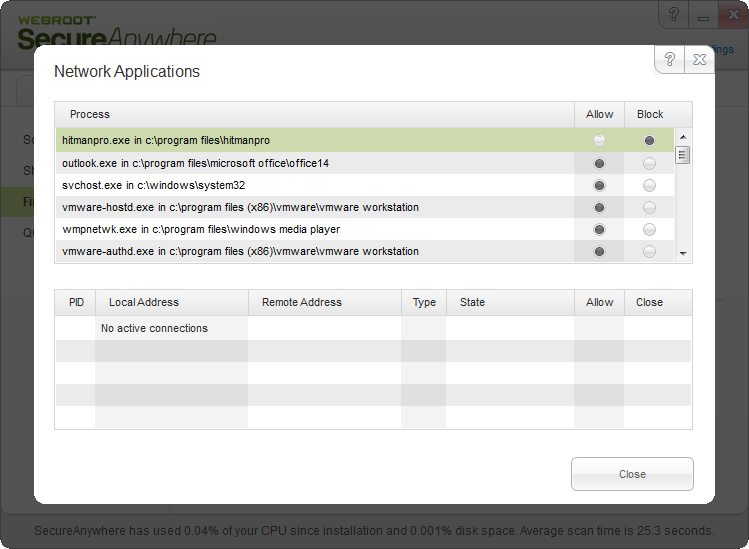
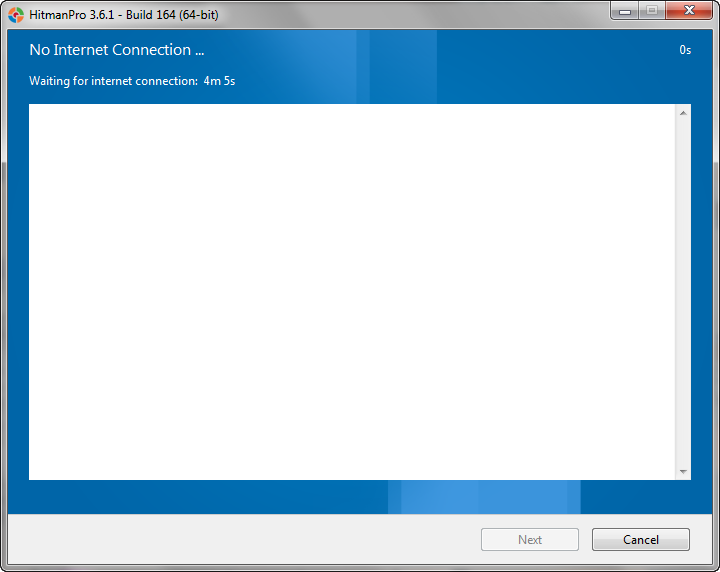
I chose vlc.exe process (VLC player) under Network applications and changed it to Block from Allow. Afterwards I had run VLC player and had triggered the update check supposing that VLC wouldn't be able to connect to the internet due to imposed the connection rule to Block. However to my surprise VLC could check for the updates.
Am I missing something as regards the firewall rules?
Is there any way how could I properly check the firewall blocks the blocked processes/applications for the outbound connections?
Thanks & regards,
pegas
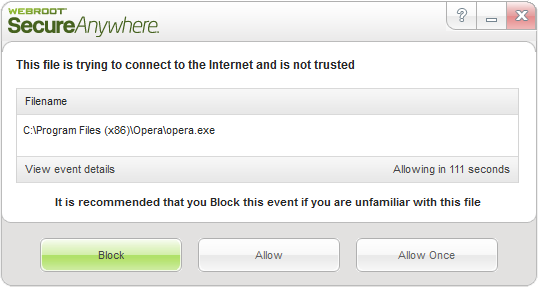
EDIT: Strange ... I changed the firewall setting to "Warn if any new untrusted process connects to the internet", chose revouninstaller.exe for instance, changed to Block and tried to check updates of Revo Uninstaller what ended up in having the blocked connections message in Revo. So now it worked how I had supposed.
However I am missing an option to add my own process/application to block. Is there any other way how to do that?
Best answer by JimM
View original