With this release we see the much requested File and Folder Overrides functionality introduced at both Global Site Manager and the Endpoint Protection management levels with some considerable enhancements to the Overrides user interface to support this new capability.
The following functionality is being released:
NEW – GSM File and Folder Overrides – This allows Global Whitelisting Overrides to be set at the file and/or folder level, in addition to the whitelisting of MD5’s.
NEW – Endpoint File and Folder Overrides - This allows Whitelisting Overrides to be set at the file and/or folder level, in addition to the whitelisting of MD5’s.
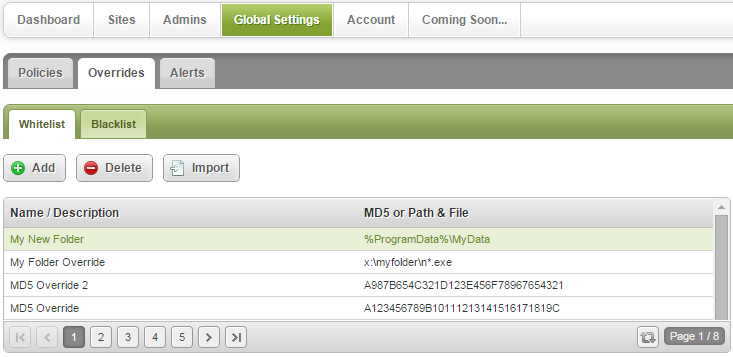
- NEW – GSM File and Folder Overrides - Global whitelist Overrides may now be set on a file or folder level as well as at the MD5 level. This allows much greater flexibility when using overrides and that multiple MD5 Overrides no longer have to be individually whitelisted as you can whitelist a whole directory. To help simplify the whitelisting of files and folders and improve clarity the Overrides tabs are now split between Whitelist and Blacklist, which will improve management and retain the current familiar look and feel.
Whitelist Overrides now appear on a separate Whitelist Tab alongside Whitelisted MD5s
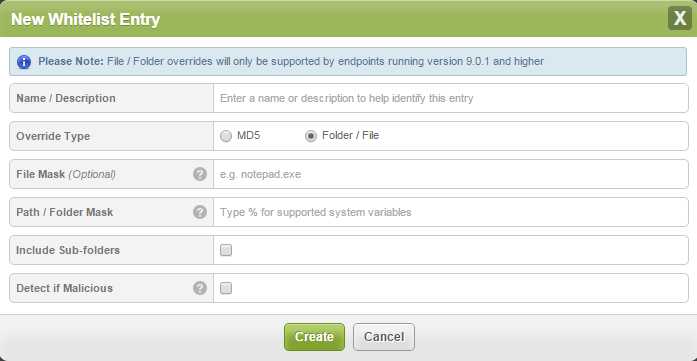
Creating a new File / Folder Whitelist Override
To create a new File or Folder whitelist override click on the ADD+ button and from the New Whitelist Entry panel select the Folder/File Override. Then…..
File Mask: Target a file or group of files by specifying a file mask with optional wildcards, for example:
- *.exe to target all executable files in the selected folder.
Path/Folder Mask: Defines the folder to target with the Override. You can specify an absolute path, for example:
- ‘x:myfolder’ or a system variable with optional path, for example
- ‘%SystemDrive%myfolder’.
Include Sub-folders: Select this if you wish to apply the override to all sub folders within a folder.
Detect if Malicious: If this setting is enabled Webroot will continue to protect against any threats originating from the whitelisted file/folder override but this selection does also disable monitoring and journaling to avoid applying monitoring and journaling to a potentially large number of files with an unknown determination. Disabling this setting provides fully trusted whitelisting that allows files to run without any Webroot protection.
IMPORTANT NOTES:
- To use file/folder Overrides you need to ensure all endpoints are running Agent version 9.0.1 or higher as earlier versions ONLY support MD5 overrides.
- Blacklist override functionality is unchanged.
- Override import functionality supports MD5 overrides only.
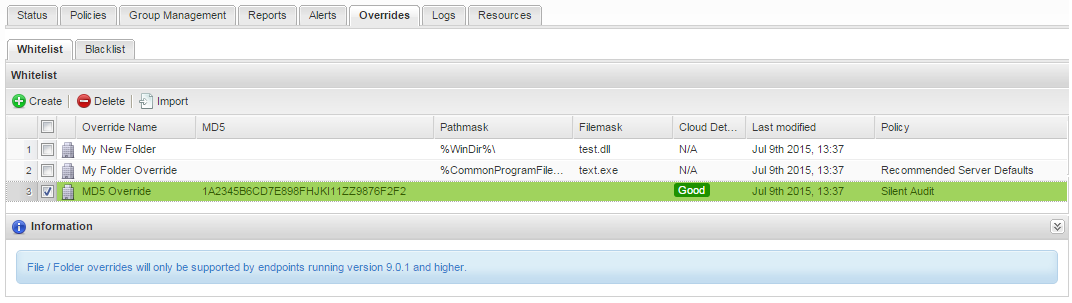
- NEW – Endpoint File and Folder Overrides – This allows users of the Standard Endpoint management console to also apply whitelisted file and folder Overrides as well as continue to use MD5 whitelisting.
Whitelist Overrides now appear on a separate Whitelist Tab alongside Whitelisted MD5s
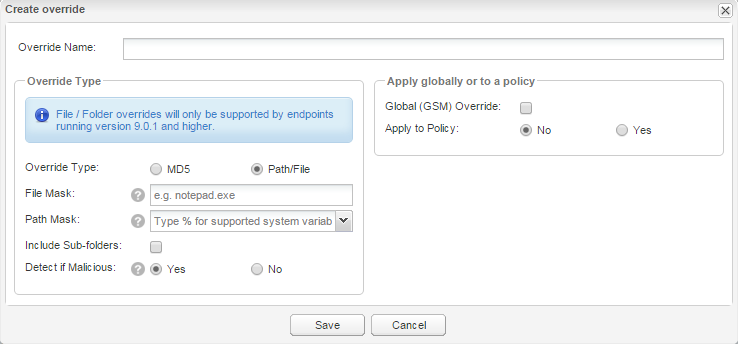
Creating a new File / Folder Whitelist Override
To create a Whitelisted File/Folder Override click on the +Create button and select the Path/File radio button.
File Mask: Target a file or group of files by specifying a file mask with optional wildcards, for example, *.exe to target all executable files in the selected folder. This will default to all files in the selected folder/path if not specified.
Path / Folder Mask: The folder to target with the override. You can specify an absolute path, for example, ‘x:myfolder’ or a system variable with optional path, for example, ‘%SystemDrive%myfolder’.
Default supported environment variables are displayed in a drop-down list however you may choose to use any variable you have setup on the target machine with the exception of user variables which are not supported. You may not use ‘%temp%’ for example as this refers to a specific users temp directory (‘username/temp/’). Wildcards are not supported.
Include Sub-folders: Select this if you wish to apply the override to all sub folders within this folder.
Detect if Malicious: If this setting is enabled Webroot will continue to protect against any threats originating from the whitelisted file/folder override but this selection does also disable monitoring and journaling to avoid applying monitoring and journaling to a potentially large number of files with an unknown determination. Disabling this setting provides fully trusted whitelisting that allows files to run without any Webroot protection.
IMPORTANT NOTES:
- To use file/folder Overrides you need to ensure all endpoints are running Agent version 9.0.1 or higher as earlier versions ONLY support MD5 overrides.
- Blacklist override functionality is unchanged.
- Override import functionality supports MD5 overrides only.
- GSM Overrides cannot be edited at the Endpoint Protection level.