According to a recent PCMag article, there's a new vulnerability that could allow a hacker to hijack your apps, taking a traditional Man-in-the-Middle (MITM) attack to potentially more malicious levels. Yair Amit from Skycure, who discovered the vulnerability, says this attack (he calls if an HTTP Request Hijacking Attack) can permanently change the behavior of apps in iOS. So how does it work? It starts with an MITM attack. And then:
"While you're connected to the the malicious network, the attacker monitors your traffic and looks for apps retrieving information from servers. Then the attacker intercepts that request and sends a 301 HTTP status code back to the application. This is a permanent redirection error, and tells the browser that the server it's looking for has been permanently moved to another location."
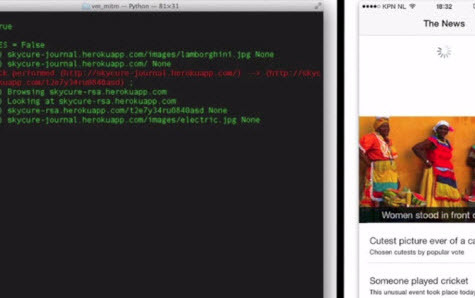
Amit goes on to explain that the vulnerable apps will then cache the change, proceeding to connect to the redirected server with no intent on stopping. While this could actually be beneficial (in terms of a faster and more reliable connection) if this is a non-malicious scenario, the problem is that the info that the app starts to load after the 301 error is coming from their server. Check out Skycure demonstration of the vulnerability:
(Source: Skycure)
Amit says that his team hasn't seen the attack in the the wild, but also pointed out how widespread it is, seemingly affecting thousand of apps. For the time being, staying safe (as possible) largely means keeping your apps up-to-date, as developers [hopefully] will start to create fixes for the vulnerable apps. If you think you've already fallen victim to this type of attack, you should uninstall the affected app and reinstall it from the app store.
The full article can be found via the aforementioned link.
(Source: PCMag)