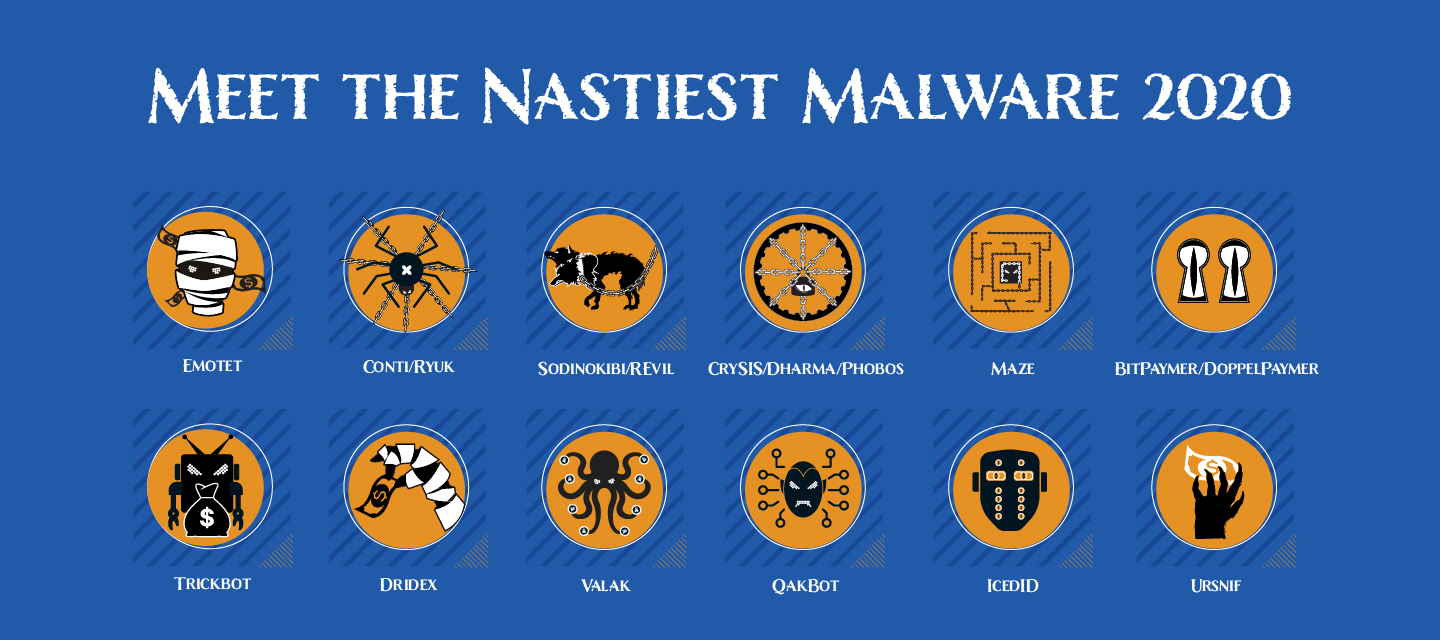
COVID-19 has absolutely dominated headlines this year, so it’s of no surprise that criminals have taken advantage of this to where most of the threat landscape this year is also heavily COVID-19 related. While this list may define payloads into different categories of malware, note that many of these bad actor groups contract work from others. This will allow each group to specialize on their respective payload and perfect it. This criminal underground community working together is what makes the threat landscape as nasty as ever.
Ransomware continues to dominate headlines of breaches and the amount of devastation they cause. The average ransom payment is now over $175k and looks to clear $200k before the end of the year. Not only are most ransomware campaigns specifically targeting businesses over consumers, but some of them are now leaking your data if you decide not to pay the ransom. This is done so that if the victim tries to not pay the ransom and sweep it under the rug, they will be ousted and open to damage of brand and fines from compliance agencies like GDPR and CCPA. This is the nastiest trend we’ve seen and it’s only growing in adoption as it has a direct impact on the victims decision to pay the ever growing ransom amounts.
Phishing is a key part to a malware campaigns effectiveness and its usage has not stopped growing since it came out decades ago. Victims falling for phishing is the first step in an infection that will lead to important credentials stolen or more payloads dropped on the machine eventually leading to ransomware. It’s only getting harder to avoid falling for phishing emails as they get better and harder to spot every year. Malicious spam emails (malspam) is so important to many of the mentioned malware campaigns below that they simply do not infect or pose any threat if the user doesn’t fall for the phishing attempt. Therefore, it’s so important for users to educate themselves on the new trends of phishing tactics.
This year is all about the pandemic and almost all the malspam phishing lures used by malware are based on COVID-19. The most common lures are around safe guidelines on how to protect yourself pretending to be from the CDC, WHO, NHO and White House asking you to download a word doc. We also saw fake pandemic stimulus lures and expect those to resurface if there is another stimulus approved. Once the word doc is downloaded from the attachment or link, it will ask the user to click the “enable content” button. This is what’s known as a macro, which if the user clicks on, will deliver the malware to their machine and is the scam that users should avoid at all costs. Macros are the most popular way criminals get victims to turn a word document into a malicious payload that can infect the entire network.

Emotet Botnet
While not a ransomware payload, but instead a botnet that is responsible for the most ransomware infections, it must be included at the top of this list – 3 years in a row now and for good reason. Even with taking regular breaks throughout the years they are the best when it comes to malspam emails into word macros that result in infection of banking trojans and ransomware. Many organizations have anti-spam technologies in place to make it more difficult for malware campaigns to make it to the inbox. Therefore, Emotet has been involved with so many partnerships with other malware groups because they are so effective and specialize at making it into the inbox. Has been seen involved with trickbot/dridex/qakbot/conti/ryuk/bitpaymer/REvil.

Conti/Ryuk Ransomware
Ryuk is no stranger and has been on this list before as ransomware operators that use Emotet and Trickbot quite a bit. Ryuk is even reported by the FBI as the most successful ransomware as far as payments in 2019. Note that the data from the FBI is ransom amounts paid as reported to the FBI and likely does not represent real world data as most victims try to sweep it under the rug and underreport. Conti has spiked in hits this year and is suspected to be the spiritual successor to Ryuk as the code of Conti looks to be based off the second version of Ryuk. While Conti has been deployed from RDP, it's not brute-forced from unsecured RDP, but instead the credentials are grabbed or phished elsewhere like from an info stealing trojan like trickbot or qakbot – likely deployed from the initial Emotet infection. These ransomware authors also operate a breach/leak site to further intimidate victims into paying the ransom.

Sodinokibi/REvil/Gandcrab Ransomware
Gandcrab and Sodinokibi were on this list last year and they’ve been keeping up infections all year. Gandcrab changed their name to Sodinokibi when the authors wanted to “retire” and then another rebranding to REvil. This ransomware as a service payload (RaaS) is available for hire as long as a cut of all successful ransoms are paid to the authors. Happy Blog is also the name of the breach/leak site created to increase victims chance of paying out and is probably the most famous one.

Crysis/Dharma/Phobos Ransomware
These ransomware payloads are almost exclusively deployed using compromised RDP credentials that are typically brute forced or easily guessed after finding them using tools (like shodan.io). All of these ransomware payloads are considered clones of the same group of malware authors and their payloads are also available for hire for a cut (RaaS). Unsecured RDP has risen over 40% since the COVID-19 pandemic which means the attack vector to which these payloads specialize has only grown. This attack vector also doesn’t require the victim to fall for any phishing attack.

Maze Ransomware
Maze ransomware has been in some big headlines this year with who they have hit. They originally started out deploying their payloads from exploit kits from insecure websites (malvertising), but they have evolved to use spam emails and RDP attacks well. Has been seen being dropped by IcedID trojan They are also considered to be the trailblazers of the new trend of stealing the data before encrypting it, to gain leverage for threatening breach/leak damage.

Bitpaymer/Doppelpaymer Ransomaware
Bitpaymer and the code fork Doppelpaymer ransomware are no strangers to this list either. They are the ransomware payload of choice and the result of the famous Dridex banking and infostealer trojan. Dridex is either dropped on the machine from emotet, or their own malspam campaign. They also joined in on the trend of stealing the data before full encryption so they could threaten breach/leak of data on the dark web to increase chance of ransom payment.

Trickbot
A very popular banking trojan and infostealer. Historically, Trickbot was just a banking Trojan meaning that its initial means of making money was through web injects to steal credentials. Now upgraded, it is typically deployed as second stage from emotet that leads to ransomware, but we've seen them without emotet this year as well. Almost always leads to eventual ransomware infection of Ryuk or Conti. Once on the machine its job is to move laterally throughout the network using exploits to propagate and gather as much credentials from infected machines as possible until domain credentials are gathered – which can take weeks or months. Since the bad actor now has full control of the environment, they will make sure that the ransomware will do the most damage and mitigations likely fail.

Dridex
Another very popular banking trojan and infostealer that has been around for years, but also now deploys ransomware like Bitpaymer/Doppelpaymer. Dridex is either dropped on the machine from emotet, or their own malspam campaign. Once on the machine its job is to move laterally throughout the network and drop dridex loaders on every machine to create persistence. Then to gather as much credentials from infected machines as possible until domain credentials are gathered – which can take weeks or months. Since the bad actor now has full control of the environment, they will make sure that the ransomware will do the most damage and mitigations likely fail.
Valak
After receiving significant updates in 2020, Valak has evolved to be a potent multi-functional malware distribution tool. Not only does it commonly distribute nasty malware such as IcedID and Ursnif, but it also has information stealing functionalities built directly into the initial infection.

Qakbot
Probably the oldest infostealing trojan still receiving updates today. Qakbot has been seen dropped by emotet, but also through it’s own malspam campaigns with links to compromised websites. It’s job is similar to Trickbot and Dridex to move throughout the network and infect the entire environment. It’s also been seen teaming up with ProLock Ransomware since it’s such an effective strategy to monetize an infected environment.

IceID
Very popular banking trojan and it's got some upgrades this year including steganographic payloads. It’s been seen associated with Trickbot, Ursnif, and Maze Ransomware.

URsnif (aka Gozi/Dreambot)
Banking trojan that has resurfaced after many years, seen dropping IcedID and is similar to the other trojans and infostealers mentioned
Mobile mentions
- Joker: This trojan has only been around since 2019, but has been growing in popularity so much that in recent months it has been found quite often on the Play Store. Joker simulates other legitimate apps to try to steal credit card information and/or banking credentials.
- CryCryptor: A ransomware found in 2020 that encrypts files on the device, but doesn’t lock the phone. This ransomware is based off the open-source ransomware CryDroid, and was masquerading as COVID-19 tracing apps.
- MobOk: A trojan that runs in the background and steals users’ info, this malware was first discovered in June 2019. This year a new variant was discovered in apps that were found and pulled off The Play Store.
- EventBot: A new Banker variant that was discovered in March of 2020. It abuses accessibility features to steal user data, as well as reads and steals SMS messages to bypass 2-factor authentication.
- Dingwe: An early Android RAT (Remote Access Tool), that was modified and found in 2020. It is capable of controlling a device remotely. Banker and Spy Agent (COVID-19 tracing apps): While these are not new malware, there have been many samples found this year of them masquerading as COVID-19 tracing apps.