Okay Webroot I want to know how good is WSA against all Ransomware with it’s Monitoring and Rollback feature as it says here: https://www.webroot.com/us/en/home/products/compare
There’s not much info I can find anywhere or even on the Webroot YouTube Channel: https://www.youtube.com/user/WebrootSoftware/videos so lets put it to bed once and for all.
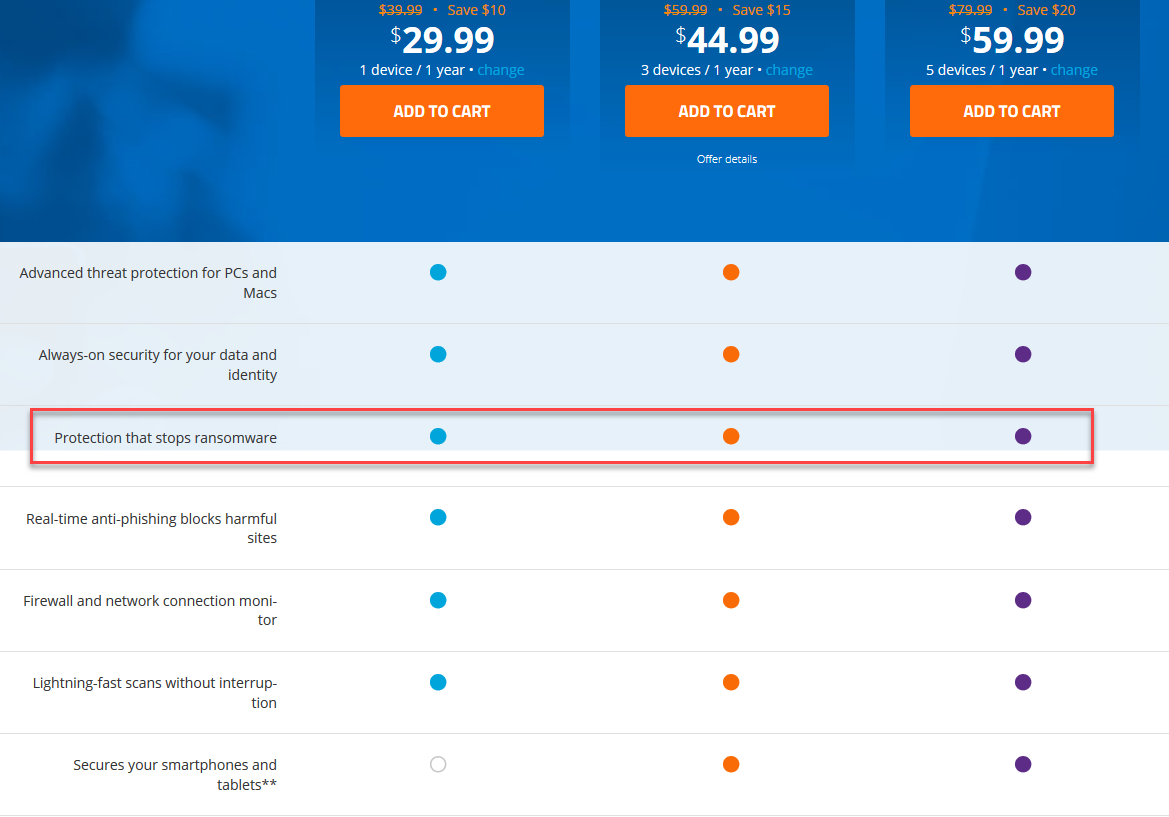
“Protection that stops ransomware”
So does it protect from Ransomware or not and please explain in detail as we want to know.
Thanks,






